There are 3 crucial names in the birth of the Blockchain but which, however, are very little known beyond the most expert circles related to this technology. The first 2 are Stuart Haber and W Scott Stornetta, who in 1991 laid the foundations on which the first functional Blockchain would be created shortly after. These bases were presented in a study called “How to time-stamp a digital document” or “How to make a time stamp on a digital document” where they sought mechanisms to improve the security of digital documents by creating time stamps that would prevent the documents from being manipulated or modified.
The system that the two finally created was the blockchain, which would contain digital documents protected with a cryptographic key that would make their manipulation practically impossible. A year later, in 1992, they incorporated into the design a fundamental part for the later arrival of the Blockchain as we know it today, the Merkle trees. The design of these trees was created by Ralph Merkle in the year 1979, in order to streamline the process of verifying large amounts of data. To create this, Merkle created a data structuring by strata where each existing node was related to a unique root associated with it called Merkle root, where each node must have a unique identifier which is called “hash” (a term that we will go deeper into in module 2). Once each node has its own hash, they are concatenated in pairs and the result of this sum is assigned a new identifier. This process is repeated until there are no more pairs to associate, resulting in the main hash or Merkle root.
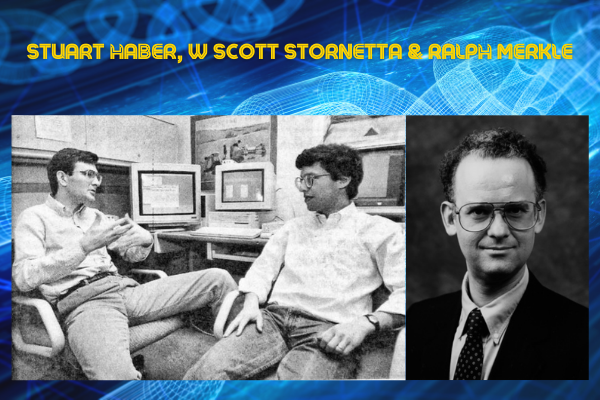
As we mentioned at the beginning, Merkle sought to speed up the verification process of large amounts of data using this system; however, not only did it achieve this, but it also managed to give the entire structure an extraordinary level of security, since, due to the way hashing processes operate, any modification, however small, of the content would result in a totally different identifier and would therefore end up modifying the root itself due to the chain effect.
As we have seen, the Merkle tree, was a key incorporation in the first blockchain design by Haber and Stornetta, thus giving Merkle a fundamental role in the creation of the Blockhchain being the third key name in the history of its birth.
The foundations of the technology were already in place, however, it would still take several years before it was finally applied for the first time. In 1998 Nick Szabo, a computer scientist and cryptographer, designed “Bit Gold” which consisted of a decentralized digital currency whose structure was based on the participation of different agents who use the computing power of a computer to solve a series of cryptographic puzzles.
When an agent in the network solves one of the puzzles, the solution is sent to a public registry and is associated with the solver. The solution, in turn, generates new coins and forms part of the next puzzle to be solved, thus creating a chain where each new link created depends on the previous one. This aspect is a fundamental part of the design, allowing all participants to verify the solutions to the puzzles and, if the majority agree, move on to the next one. The problem for Szabo started when designing the digital currency transactions, as he ran into the wall of “double spending”, which is an attack by which a cybercriminal can use the same currency as many times as he wants due to the very decentralized design of the network. This is why Bit Gold never became a reality, although, as we shall see, it laid the groundwork for another digital currency that would emerge a decade later. It was not until 2004 when computer scientist and crypto activist Hal Finney created a system called “Reusable Proof of Work” or RPoW, which solved the double-spending problem that Szabo ran headlong into.

The main design of the RPoW is to perform a moderately difficult job on the client side and easy to verify on the server side. The proof of work performed is called a “POW token” and has a limited form of sequential reuse. This allows a POW token to be used once, then Hal Finney. Source en.wikipedia.org 9 exchange it for a new one that could be used again only once and then exchanged again in a process that we can repeat as many times as we want. This is why the RPoW solved the problem of double spending since, for example, if a sender wanted to send a coin to a recipient, as soon as that coin was sent to the receiver the sender would spend the use of his coin and would not be able to use it again. RPoW was the last piece of the puzzle that was missing so that, 4 years later, a link appeared in a cryptography forum redirecting to a white paper written under the pseudonym of Satoshi Nakamoto entitled “Bitcoin: A Peer-to-Peer Electronic Cash System”.


One thought on “BLOCKCHAIN COURSE UNIT 01: START OF OF THE BLOCKCHAIN”